Audit trails are critical for compliance, especially in industries like finance and crypto. They document every action, ensuring transparency and meeting regulations like AML, FATCA, and CRS. Missing or tampered records can lead to fines, penalties, or operational inefficiencies. Here’s what you need to know:
- Key Elements: Include user identity, timestamps, actions, and cryptographic proof.
- Tamper-Proofing: Use append-only storage and technologies like SHA-256 or blockchain.
- Time Accuracy: Sync systems with trusted sources like NTP and standardize on UTC.
- Access Control: Restrict log access with unique logins, RBAC, and multi-factor authentication.
- Automation: AI hedge fund administration tools can monitor logs, flag issues, and reduce compliance costs by up to 84%.
Audit Trail and Role of Auditor – 10 Important FAQs, Reporting Obligations, How to verify
sbb-itb-9792f40
Core Elements of Effective Audit Trails
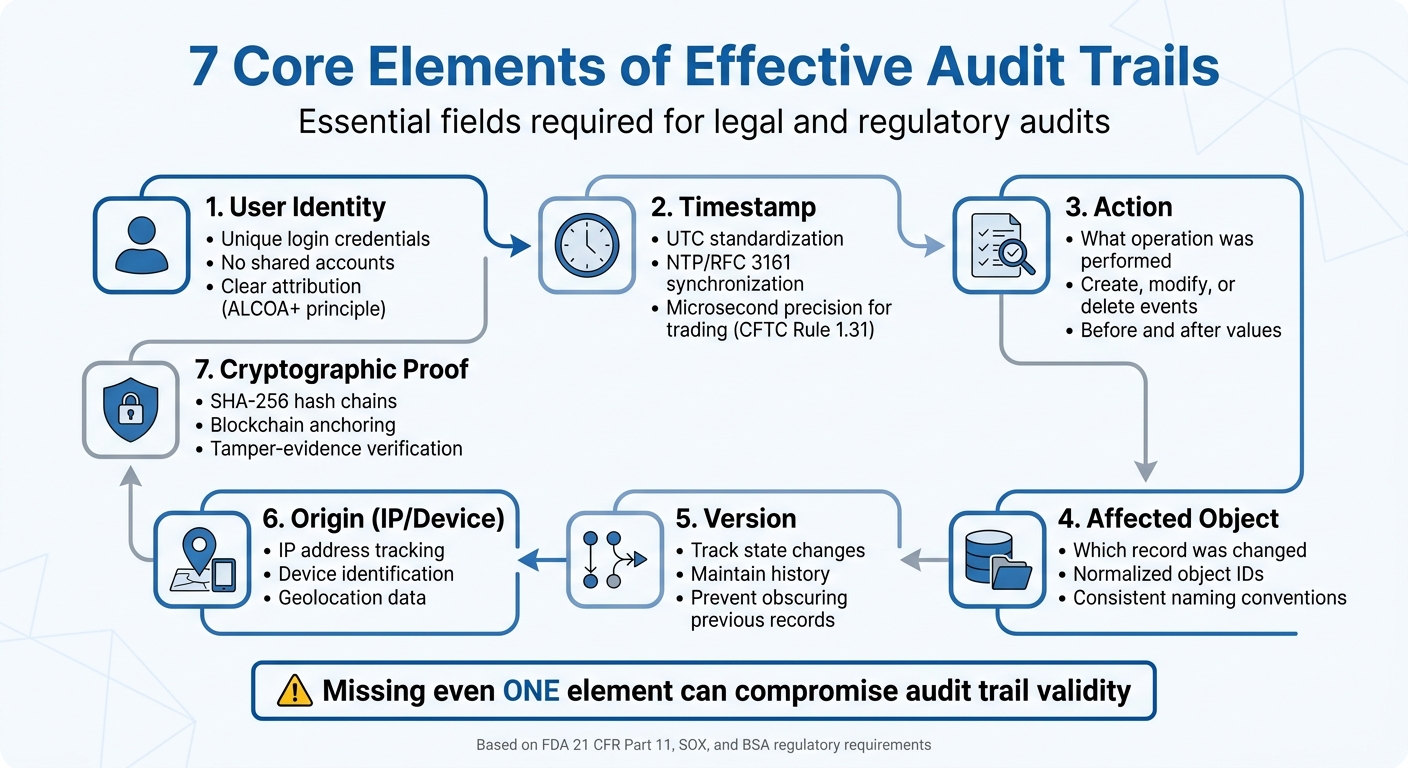
7 Core Elements of Effective Audit Trails for Regulatory Compliance
An effective audit trail must capture seven key fields: user identity, timestamp, action, affected object, version, origin (IP/device), and cryptographic proof. These fields ensure that the documentation holds up in legal or regulatory audits. Missing even one of these elements can compromise its validity.
The FDA‘s 21 CFR Part 11, Section 11.10(e), emphasizes the importance of secure and time-stamped audit trails:
Use of secure, computer-generated, time-stamped audit trails to independently record the date and time of operator entries and actions that create, modify, or delete electronic records.
This isn’t just a healthcare standard. Financial institutions under SOX must retain audit trails for seven years, while BSA regulations require five years of record retention for wire transfers over $3,000. Additionally, users must not have the ability to alter or remove records of their own actions. These principles lay the groundwork for the best practices discussed below.
Data Integrity and Tamper-Proofing
Audit logs need to be stored in an append-only format, ensuring that records cannot be altered or deleted, even by system administrators. This isn’t just a recommendation – it’s a regulatory requirement. As ECOSIRE points out:
An audit log that can be modified by anyone – including system administrators – has limited value as compliance evidence.
The distinction between tamper-resistance and tamper-evidence is crucial. While tamper-resistance makes changes difficult, tamper-evidence ensures that any alterations are mathematically detectable. This is achieved through technologies like SHA-256 hash chains or blockchain, which meet the legal standards for admissibility.
WORM (Write Once, Read Many) storage solutions, such as AWS S3 Object Lock or Azure Immutable Blob Storage, provide immutability by preventing deletion of logs. For organizations managing high-value transactions, blockchain anchoring takes this a step further by linking audit trails to a public ledger. This ensures third-party verifiable proof, even if the original vendor ceases operations.
The sheer volume of data can be staggering. For instance, a mid-size ERP system handling 10,000 transactions daily generates over 500,000 audit log entries each day. To manage this, automated database triggers or ORM hooks should capture state changes – both before and after values – without relying on manual developer input.
Time Synchronization and Accuracy
Accurate timekeeping is critical for sequencing events and maintaining record integrity. Trusted time sources, such as NTP (Network Time Protocol) or RFC 3161, ensure precise timestamps. Since system-generated timestamps can be manipulated, permissions must prevent users and administrators from altering system clocks.
To avoid confusion, standardize on UTC across all systems, especially for global operations. In specialized fields like high-frequency trading, the CFTC Rule 1.31 mandates microsecond-level precision for electronic trading records. Even in less demanding environments, clock drift between systems must be monitored and corrected within acceptable limits.
Regular reconciliation checks are essential to detect gaps, overlapping timestamps, or sequence errors caused by synchronization failures. Organizations should document their authoritative time source and the frequency of synchronization. For high-value or legally sensitive records, independent time verification through qualified trust service providers (e.g., under eIDAS in the EU) or RFC 3161 authorities strengthens the credibility of the records.
Access Control and User Authentication
While technical safeguards protect the integrity of audit logs, restricting access ensures accountability. Every user must have a unique login to enable clear attribution of actions. Shared or generic accounts are a compliance red flag because they make it impossible to trace individual activity, violating the "Attributable" principle of ALCOA+.
Access to the logs themselves must be tightly controlled using Role-Based Access Control (RBAC) and secured with multi-factor authentication. Additionally, access to the logs should be logged separately to prevent administrators from erasing evidence of their own actions. Regulatory standards often require that audit trail reviews be conducted by personnel independent of system administration. This "four-eyes" principle ensures that those with high-level access cannot cover up unauthorized changes.
Monitoring authentication patterns can help identify potential breaches. Examples include repeated login failures, simultaneous logins from distant locations, or unusual activity from service accounts. Automated alerts should flag high-risk events like privilege escalations, configuration changes, or after-hours access. Regular testing must confirm that even system administrators cannot delete or modify audit entries, aligning with regulations like 21 CFR Part 11.
Standardizing Audit Trail Processes
Even with well-designed technical systems, consistent procedures are essential for effective audit trails. Without standardization, reconstructing events during regulatory reviews can become impossible. The issue often isn’t missing data but rather inconsistent processes that fall apart under scrutiny. Considering that noncompliance costs firms around $15 million, investing in standardized procedures upfront is a smart move to avoid costly penalties.
Standardization ensures that event streams are transformed into evidence that meets regulatory requirements. This involves defining which systems are in scope (like ERP, LIMS, or eDMS), identifying critical record types, and specifying which events – such as configuration changes, authentication attempts, or data exports – must be logged. By addressing gaps in these areas, standardized processes help ensure that every logged event can withstand regulatory examination.
Developing Standard Operating Procedures (SOPs)
SOPs provide a structured approach to log management across the organization. They should clearly define roles and responsibilities, ensuring proper segregation of duties. For example, the individual responsible for reviewing audit trails must not be the same person managing the system. This "four-eyes" principle prevents conflicts of interest and aligns with regulatory expectations for independence.
Risk-based review schedules are critical. High-risk systems might require daily or weekly reviews, moderate-risk systems monthly, and low-risk systems quarterly. For instance, a fund administrator managing anti-money laundering (AML) compliance would review investor onboarding and transaction monitoring systems daily, while internal HR systems might only need quarterly reviews.
SOPs should also include steps to verify log integrity, such as checking for completeness, sequence continuity, and consistent timestamps using cryptographic hashes or digital signatures. Escalation protocols are equally important – when anomalies are detected, the SOP should guide reviewers through root-cause analysis (e.g., using the "5 Whys" technique) and documentation in Corrective and Preventive Actions (CAPA) reports.
To further safeguard compliance, configure audit systems to generate alerts for logging failures, storage limits, unauthorized system restarts, or shutdowns. These automated notifications help identify and address gaps in the audit trail before they escalate into compliance violations.
Implementing Consistent Data Structures
Consistent processes go hand-in-hand with structured data. Standardized formats make it easier to analyze and report on audit trails. Data normalization – ensuring uniformity in usernames, object IDs, and event codes – enables accurate comparisons across different systems. Without this, tracking a single user across platforms might be impossible if they appear as "jsmith", "john.smith@company.com", and "Smith, John" in different environments.
Every audit entry should adhere to ALCOA+ principles (Attributable, Legible, Contemporaneous, Original, Accurate, Complete, Consistent, Enduring, Available) to meet regulatory standards. For example, recording "before and after" values for every change ensures compliance with FDA 21 CFR Part 11, which mandates that "record changes shall not obscure previously recorded information". If a fund administrator updates an investor’s tax classification for FATCA reporting, the audit trail must show both the original and updated classifications, along with details of who made the change and when.
Using machine-readable formats like JSON or CSV simplifies filtering, searching, and reporting during audits. Regularly testing your audit trail by reconstructing events can help identify any gaps in standardization. This proactive approach ensures that your processes address compliance challenges before regulators have a chance to flag them, reducing the risk of costly violations.
Reviewing and Analyzing Audit Trails
Having standardized processes is a good start, but it’s the regular reviews that truly make those processes effective for compliance. The difference between staying compliant and facing a regulatory issue often boils down to whether someone is actively reviewing the logs – and knowing exactly what to look for.
Routine and Incident-Based Reviews
How often you review systems should depend on the level of risk they carry. High-risk areas, such as critical financial transactions or changes to privileged access, need daily or weekly reviews. Moderate-risk systems can be checked monthly, while low-risk ones might only require quarterly attention. For example, AML (Anti-Money Laundering) administrators should prioritize frequent reviews of investor onboarding and transaction monitoring systems.
In addition to routine reviews, incident-based analysis is essential when specific events occur. These might include security breaches, system updates, or major audit findings. A notable example occurred in November 2025, when the Swedish Police and Financial Intelligence Center (FINUC) worked together to disrupt criminal financial activities. By analyzing transaction patterns and inconsistencies across major banks, they managed to shut down approximately 400 bank accounts and recover 30 million SEK (around $2.8 million USD). This success was due to their ability to act swiftly through event-driven analysis rather than waiting for the next scheduled review.
During any review, log completeness is key. Check for missing sequence numbers, consistent timestamps, and unexpected gaps in event volumes. Keep an eye out for behavioral red flags, such as repeated failed login attempts, unauthorized activity during off-hours, or bulk edits to critical records. To separate legitimate actions from real anomalies, reconstruct timelines by linking audit trail entries to external evidence, like change tickets or authorized activities.
Routine reviews can be further strengthened by implementing a dual-review process to ensure that anomalies are thoroughly examined.
Dual-Review and Root-Cause Analysis
When routine or incident-based reviews flag potential issues, a dual-review process becomes vital. Having someone independent of system administration review the audit trails ensures proper segregation of duties, reduces conflicts of interest, and improves accuracy through an additional layer of oversight.
Once anomalies are identified, classify them by risk level: critical (potentially impacting data integrity), major (indicating control weaknesses), or minor (relating to documentation errors). To dig deeper, use root-cause analysis techniques like the "5 Whys" method. For example, if an unauthorized configuration change appears in the audit trail, asking "why" repeatedly might reveal that the root issue was inadequate role-based access controls rather than intentional wrongdoing.
Document your findings in Corrective and Preventive Actions (CAPA) reports. These reports should detail what happened and outline steps to prevent it from happening again. Actions might include revoking access, rolling back unauthorized changes, or updating protocols. This closed-loop process turns audit trail reviews into proactive risk management, ensuring every anomaly is investigated and resolved. Together, these methods strengthen compliance efforts and enhance operational transparency.
Using Automation for Compliance
Relying on manual processes for compliance can be both expensive and error-prone. Financial institutions, on average, spend $287,000 annually on fixing errors, and 68% of firms face penalties for mistakes related to FATCA and CRS due to outdated workflows. Automation steps in to solve these issues by handling repetitive tasks and minimizing human error, creating a more streamlined and real-time approach to compliance.
Automated Monitoring and Alerts
Automated systems continuously monitor audit trails and conduct rules-based testing on datasets before regulatory submissions. Unlike traditional periodic reviews, these tools identify issues – like missing Tax Identification Numbers (TINs) or suspicious activities – as they happen. For example, AI platforms compare investor self-certifications against IRS and OECD standards with an impressive 99.1% accuracy, catching errors that manual checks often miss.
The time savings are dramatic. Manual validation for FATCA and CRS can take over 200 hours per month, but AI tools cut this down to just 10 hours. This allows compliance teams to focus on more complex tasks rather than routine data entry. If the system detects issues – such as outdated self-certifications, which occur in 18% of high-value accounts – it sends instant alerts, enabling teams to resolve problems before submission deadlines.
API-based verification systems also create tamper-resistant audit trails, complete with ISO 8601 timestamps and watermarked visual proof. Joe Salvatore, Chief Risk Officer at Idea Financial, highlighted the transformation:
This was an area of the business that was completely manual still… sort of the Achilles heel.
These systems even store screenshots in WORM (Write Once, Read Many) storage, ensuring records remain intact, especially since vendor URLs often expire within 3–30 days.
AI Integration for Efficiency
Beyond monitoring, AI integration takes compliance to the next level by identifying complex patterns and adapting to evolving regulations without the need for constant updates. These tools validate individual records, uncover connections between accounts, detect unusual behaviors, and reduce reporting rejection rates by 85%. They also slash compliance costs by 84% per form.
The financial benefits are significant. Large institutions using automation have reduced remediation costs by $4.2 million annually. But it’s not just about saving money – AI also addresses governance concerns, which regulators are increasingly focusing on. As Jersey’s Comptroller of Revenue emphasized:
AEOI failures are no longer treated as administrative slip-ups, but as governance weaknesses.
Automated systems provide detailed digital paper trails, proving proper oversight and compliance.
Implementing these systems typically involves a phased rollout. API connectivity takes about 1–2 weeks, rules configuration 2–3 weeks, and parallel testing 3–4 weeks. Costs for cloud-based solutions start at around $15,000 per year for up to 10,000 accounts, while enterprise platforms with multi-jurisdiction support can exceed $75,000 annually. Considering that manual processes carry an average penalty risk of $70,000, compared to just $2,500 with automation, the investment quickly pays off – especially with new regulatory frameworks like CRS 2.0 and crypto-asset reporting set to launch in 2026.
Best Practices from Charter Group Fund Administration
Compliance Support for AML, FATCA, and CRS
After establishing solid audit processes, effective compliance requires tailored support from fund administrators. Charter Group Fund Administration extends its expertise to manage compliance across various regulatory frameworks, such as AML, FATCA, CRS 2.0, and the Crypto-Asset Reporting Framework (CARF). Operating in prominent offshore jurisdictions like the Cayman Islands, the firm efficiently handles evolving regulations, including the 2026 Cayman FATCA and CRS updates, which introduce earlier deadlines and expanded crypto asset reporting requirements. Charter Group also provides independent reviews of fees, NAV, and returns, ensuring funds maintain their integrity. As the firm highlights:
Having an independent party calculate returns enhances the integrity of your fund and reported returns.
Secure and Transparent Reporting
Charter Group’s reporting solutions, built on automated platforms, prioritize both security and transparency. By implementing advanced security protocols such as OAuth 2.1/PKCE, mTLS, TLS 1.3, and AES-256 encryption, the firm safeguards sensitive fund data during transmission and storage, fully aligning with SEC Regulation S-P requirements for breach notifications. Transparency is further bolstered through clear fee disclosures, standardized reporting formats, and regular audits, eliminating hidden costs and fostering investor confidence.
The firm’s investor portal offers real-time access to fund data while employing strict Role-Based Access Control (RBAC) to ensure only authorized users can view sensitive information. For crypto-asset funds, Charter Group addresses unique challenges like specialized valuations and fee structures specific to blockchain-based assets and derivatives.
The firm’s commitment to responsiveness and accuracy has earned praise from industry leaders. Richard Fish, Director at Bennelong Long Short Equity Management, remarked:
Under Brian’s leadership, the administration service his firm provided was always responsive, timely and accurate. He actively sought to add value, and was always highly professional.
Similarly, Lawrie Chandler, Director at Edale Group, shared:
The Charter Group team provide the administration for a Cayman Islands offshore fund for an advisory client of Edale. Their systems and day to day business operation and support were first rate.
These practices demonstrate how Charter Group Fund Administration combines secure, real-time reporting with rigorous compliance to deliver exceptional service.
Conclusion
Audit trails are the backbone of regulatory compliance, capturing a detailed record of digital actions to meet strict regulations. Without them, organizations expose themselves to serious risks. For example, gaps in audit trails were found in 35% of data breach incidents, and 78% of compliance audits flagged these gaps as a major control deficiency. Additionally, tax evasion costs governments around $492 billion annually, highlighting the importance of robust audit trails in the 120+ jurisdictions that have adopted the Common Reporting Standard.
Effective compliance starts with clear and precise audit entries that document who, what, when, and why. To achieve this, organizations should synchronize timestamps across systems, eliminate shared user accounts for proper accountability, and use cryptographic tools to detect tampering. Secure, automated, time-stamped audit trails must independently log all operator actions – whether creating, modifying, or deleting electronic records.
Automation and standardization play a key role in improving efficiency and accuracy. Companies leveraging automated systems report detecting incidents 36% faster than those relying on standard application logs. Automated monitoring can flag anomalies like repeated failed login attempts, unauthorized deletions, or suspicious access patterns, enabling teams to respond swiftly.
Using a risk-based approach to manage audit trails helps allocate resources effectively. High-risk systems, such as those handling financial or GMP data, may require daily or weekly reviews, while lower-risk systems can be reviewed quarterly. Regular tabletop exercises, like reconstructing a random transaction end-to-end within 30 minutes, ensure your audit trail is always ready for inspection.
Specialized support can further strengthen compliance efforts. For instance, Charter Group Fund Administration demonstrates how a well-designed audit trail framework can balance regulatory compliance with operational efficiency. Their approach incorporates cryptographically secured reporting and independent NAV reviews, ensuring alignment with global regulatory expectations for AML, FATCA, and CRS compliance.
FAQs
What makes an audit trail legally defensible?
A legally defensible audit trail needs to meet strict standards to ensure it holds up under scrutiny. It must be tamper-evident, complete, and accurate, aligning with relevant regulatory requirements.
Key aspects include:
- Chronological records: Maintain a clear timeline of events to track actions step by step.
- Protection against unauthorized changes: Safeguard the data to prevent tampering or alterations.
- Secure storage: Ensure data is stored in a way that allows for easy retrieval and verification when needed.
Additionally, thorough documentation and adherence to retention policies are critical. These practices help preserve the audit trail’s integrity and ensure its reliability when examined.
How can we prove logs weren’t modified after creation?
To ensure logs remain unaltered, rely on tamper-evident and cryptographically secure techniques. Audit trails should be immutable, include time stamps from a trusted source, and operate independently of manual interference. Methods like cryptographic hash chains (such as SHA-256) help verify log integrity, while blockchain anchoring adds an external layer of verification to detect any changes. These approaches offer reliable proof that logs haven’t been modified after being created.
How often should audit trails be reviewed for AML, FATCA, and CRS?
Audit trails for AML (Anti-Money Laundering), FATCA (Foreign Account Tax Compliance Act), and CRS (Common Reporting Standard) should be reviewed using a risk-based approach. Here’s a general guide:
- High-impact systems and records: Review these daily or weekly, as they carry the greatest risk.
- Moderate-risk areas: A monthly review is typically sufficient to monitor compliance without overburdening resources.
- Low-risk areas: Quarterly reviews are appropriate for these, given their lower likelihood of issues.
Make sure to tailor the review frequency to match your organization’s unique risk profile and compliance obligations. This helps maintain accuracy and ensures you’re meeting regulatory standards effectively.
