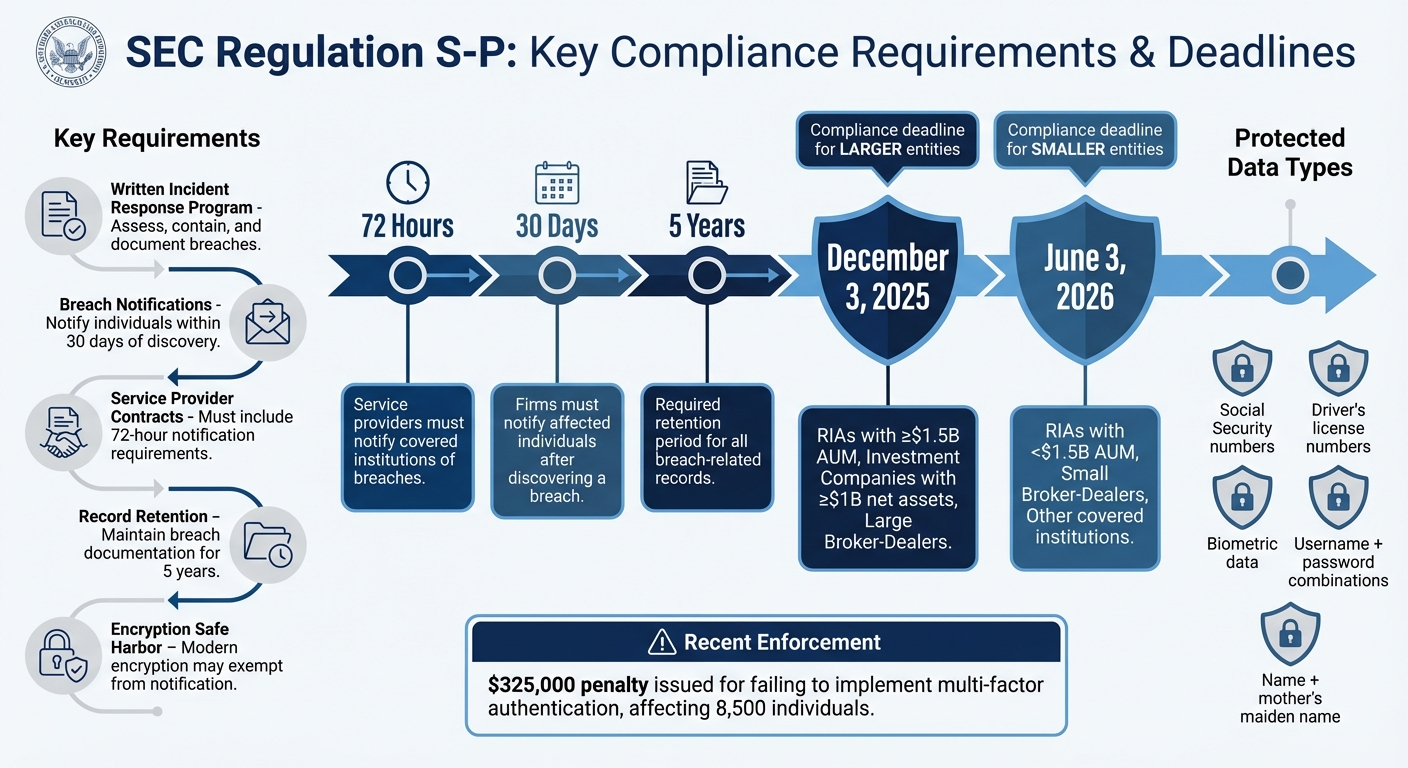
The SEC‘s 2024 updates to Regulation S-P bring critical changes to cybersecurity compliance for broker-dealers, investment companies, registered advisers, and transfer agents. Here’s what you need to know:
- Breach Notifications: Firms must notify affected individuals within 30 days of discovering a breach involving sensitive information (e.g., Social Security numbers, login credentials). Service providers must inform firms within 72 hours of identifying incidents.
- Incident Response Plans: Covered entities must implement written response programs to assess, contain, and document breaches, retaining records for 5 years.
- Encryption Rules: If compromised data is encrypted with modern protocols, notification may not be required.
- Compliance Deadlines: Larger entities must comply by December 3, 2025, while smaller ones have until June 3, 2026.
These rules aim to standardize breach responses, protect sensitive investor data, and ensure timely communication. Firms should act now to meet requirements and avoid penalties.
SEC Regulation S-P Compliance Timeline and Key Requirements 2025-2026
Data Breach Notification Guide for Beginners
sbb-itb-9792f40
Regulation S-P Amendments Explained
The updated Regulation S-P introduces a broader definition of "customer information" and requires all covered institutions and their service providers to implement a written incident response program. This program must include clear procedures for assessing and containing breaches. Additionally, firms are now required to document their vendor monitoring processes, report breaches within 72 hours, and retain all breach-related records for at least five years.
These changes align with the SEC’s heightened focus on cybersecurity, emphasizing the importance of breach notification within fund administration.
Definitions and Triggering Events
The amended rules provide detailed criteria for when breach notifications are necessary.
Sensitive customer information is defined as any data that could pose a reasonably likely risk of significant harm or inconvenience to an individual if compromised. This includes two key categories:
- Uniquely identifying information: Examples include Social Security numbers, driver’s license numbers, or biometric data.
- Authenticating information: This could be a username paired with a password, or a name combined with a mother’s maiden name.
A breach triggers a notification requirement if sensitive customer information is accessed – or likely accessed – without authorization. Unless a firm conducts a reasonable investigation and documents why the breach is unlikely to result in significant harm or inconvenience, notification is presumed necessary. Factors to consider include risks like identity theft, fraud, harassment, physical harm, or credit-related issues.
For instance, if an unencrypted email containing investor tax IDs and bank account details is accidentally sent to the wrong recipient, the firm must notify affected individuals within 30 days.
However, there is an encryption safe harbor. If compromised information is encrypted using modern algorithms and secure protocols, notification is generally not required. As the SEC explains (via Davis Wright Tremaine):
"Given the computational complexity involved in deciphering information encrypted using modern encryption algorithms and secure procedures, the compromise of such encrypted information would generally not give rise to ‘a reasonably likely risk of substantial harm or inconvenience.’"
Notification Timelines
The amendments also establish specific timelines for notifying breaches.
Service providers are required to inform the covered institution within 72 hours of discovering a breach, giving firms sufficient time to investigate and meet their notification responsibilities.
Compliance deadlines depend on the size of the entity:
- Larger entities: Registered investment advisers managing over $1.5 billion in assets or broker-dealers with total capital exceeding $500,000 must comply by December 3, 2025.
- Smaller entities: These firms have until June 3, 2026 to meet the new requirements.
How to Notify Customers After a Breach
When a breach occurs, companies must act quickly to meet legal requirements and provide clear, detailed notifications to affected customers. Below, we’ll break down the notification process and what needs to be included.
The 30-Day Notification Requirement
Companies are required to notify individuals affected by a breach within 30 days of discovering it. This countdown starts the moment the company becomes aware of the breach – or reasonably suspects one – not when the investigation is wrapped up.
Notification is mandatory unless a thorough investigation proves there’s minimal risk. If the compromised data is unlikely to cause harm or inconvenience, and this can be documented, notification may not be necessary. However, if a company can’t pinpoint exactly who was impacted, it becomes crucial to use comprehensive customer data mapping to identify everyone whose information might have been involved.
Required Notification Content
Once the notification deadline is met, the message itself becomes the focus. It needs to be clear, direct, and provide customers with the information they need to act.
| Required Element | What to Include |
|---|---|
| Incident Description | A plain explanation of what happened during the breach |
| Data Types Affected | Specific details about the compromised data (e.g., Social Security numbers, credentials) |
| Protection Steps | Practical advice on how individuals can protect themselves |
| Contact Information | Direct contact details for the company |
| FTC Reporting | A suggestion to report the breach to the Federal Trade Commission |
| Protective Services | Information on any identity-theft protection or credit monitoring services offered |
The notice should also guide customers on handling identity theft and outline any protective services, such as credit monitoring, that the company is providing.
It’s important to note that while fund administrators might help draft or deliver these notices, the covered entity is legally responsible for any mistakes or omissions. To avoid issues, companies should establish clear communication protocols and review processes well before a breach occurs.
How Fund Administrators Must Adapt
To align with the SEC’s updated rules, fund administrators need to rethink their approach to incident response, compliance, and AI hedge fund administration. These changes influence how they manage investor data, handle security breaches, and collaborate with the funds they support. This means reevaluating data protection strategies and formalizing protocols to ensure compliance.
Building Incident Response Programs
Adhering to breach notification protocols requires fund administrators to bolster their incident response strategies proactively.
Administrators should create written incident response plans that detail how to detect, respond to, and recover from breaches. These plans should include actionable steps like isolating compromised systems, rotating private keys, and updating administrator passwords immediately upon detection of an issue. Proper documentation is key, ensuring that these procedures are both clear and executable.
Additionally, all breach assessments must be retained – even if a notification is not triggered – and these records should be kept for five years. This ensures accountability and compliance over time.
One critical requirement is the 72-hour reporting rule for third-party vendors, such as cloud hosting or data storage providers. Contracts with these vendors must include provisions mandating breach notifications within this timeframe. This is essential for covered entities to meet their own 30-day notification deadline for affected individuals.
To prepare for potential incidents, administrators should conduct tabletop exercises. These scenario-based drills help staff understand escalation procedures, clarify decision-making authority, and define roles during a breach.
Integrating Compliance Services
Incident response measures must also be effectively integrated into broader compliance operations.
Fund administrators need to go beyond simply adding new steps to their processes. Instead, they should reassess how customer data flows through compliance workflows to align with enhanced cybersecurity standards. This involves refining data mapping to ensure administrators know where sensitive information is stored and who has access to it. Such visibility is critical for both preventing breaches and responding effectively when they occur.
Service provider agreements should also be updated to include specific data-security responsibilities and the 72-hour breach notification requirement. Administrators serving as third-party providers themselves must be ready to meet these contractual obligations to remain compliant with SEC regulations.
Charter Group Fund Administration, for example, offers compliance support services such as AML, CRS, and FATCA, which help clients navigate these new requirements. Their expertise is particularly valuable for funds operating in offshore jurisdictions like the Cayman Islands, ensuring they meet the SEC’s stringent cybersecurity standards while maintaining operational efficiency.
Compliance Deadlines and SEC Enforcement
Important Compliance Dates
The SEC has set two key deadlines for compliance, depending on the size of the entity:
| Entity Category | Definition Criteria | Compliance Deadline |
|---|---|---|
| Larger Entities | RIAs with ≥ $1.5B AUM; Investment Companies with ≥ $1B net assets; Large Broker-Dealers | December 3, 2025 |
| Smaller Entities | RIAs with < $1.5B AUM; Small Broker-Dealers; Other covered institutions | June 3, 2026 |
Tonkon Torp LLP emphasizes that larger advisers must meet the December 3, 2025 deadline. However, all firms should begin their compliance efforts immediately, as the SEC Division of Examinations has made this a priority for Fiscal Year 2026.
Recent SEC Enforcement Actions
The SEC is actively enforcing these new cybersecurity standards, requiring firms to demonstrate operational proof of their security measures. For example, a dual-registered RIA and broker-dealer faced a $325,000 penalty for failing to implement multi-factor authentication and update its identity theft prevention program. This lapse left 8,500 individuals vulnerable to credential-harvesting email attacks.
In addition, the SEC is paying close attention to firms with distributed structures, such as those using independent contractor models or managing multiple branch offices. These firms must ensure that enterprise-wide security policies are consistently applied across all locations. Examiners are also checking whether firms have updated their Regulation S-ID programs to address modern threats like phishing and email account takeovers, rather than relying on outdated policies. These enforcement actions highlight the need for fund administrators to strengthen their cybersecurity measures and incident response strategies.
Preparing for SEC Cybersecurity Compliance
What Fund Administrators Need to Know
With the June 3, 2026 deadline approaching, fund administrators need to establish a solid compliance framework. A key part of this involves setting up incident response programs capable of detecting, responding to, and recovering from unauthorized access to customer information. These programs must include clear steps for assessment, containment, and notification.
The definition of protected data has broadened. Administrators must now safeguard not only the customer data they collect but also information received from other financial institutions. This means mapping out how investor data flows through their systems to pinpoint and secure sensitive information.
Another priority is managing service providers effectively. Administrators will need to update vendor agreements to require breach notifications within 72 hours and ensure contracts grant audit rights. Elizabeth Cope, CPA, CEO & Lead Consultant at SEC Compliance Solutions LLC, highlights the importance of these changes:
"The 2024 amendments to Regulation S-P mark a significant shift in how investment advisers must approach data protection and breach response".
Additionally, firms will need to keep detailed records of breach responses for at least five years.
As these compliance requirements grow more stringent, fund administrators must remain alert to further regulatory changes on the horizon.
Adapting to Future Regulatory Changes
Looking beyond immediate compliance, fund administrators must prepare for regulations that continue to evolve in response to advanced cyber threats. The SEC is working to align Regulation S-P with federal standards like the FTC’s Safeguards Rule, aiming to create consistent minimum requirements. One way to stay ahead is by conducting tabletop exercises. These simulations of breach scenarios involving non-public customer information can help uncover procedural weaknesses before a real incident occurs.
The rise in cyber threats is impossible to ignore. In insourced environments, the frequency of cyberattacks surged from 39% in 2022 to 77% in 2023, with the severity of attacks climbing from 58% to 87% over the same period. Malicious actors are also using generative AI tools like WormGPT to create more advanced phishing emails and attack code. This makes continuous monitoring and regular updates to security protocols absolutely essential.
FAQs
What counts as “discovery” of a breach for the 30-day clock?
When a covered entity becomes aware – or reasonably should have been aware – that a data breach has occurred or might occur, the clock starts ticking. This marks the beginning of the 30-day notification period. Staying alert to potential breaches is crucial for ensuring compliance with SEC regulations.
When does the encryption safe harbor actually apply?
The encryption safe harbor comes into play when a cybersecurity incident is deemed material, meaning it must be disclosed within four business days. This applies to incidents that have a meaningful impact on investors, such as data breaches or disruptions to operations. The goal is to ensure stakeholders are informed promptly and transparently about critical cybersecurity events.
How should firms update vendor contracts for the 72-hour rule?
Firms need to update vendor contracts to align with the SEC Regulation S-P’s 72-hour breach notification rule. These contracts should spell out specific timelines, outline incident response responsibilities, and define detailed reporting processes. This ensures vendors are fully prepared to meet the required standards without delays.
