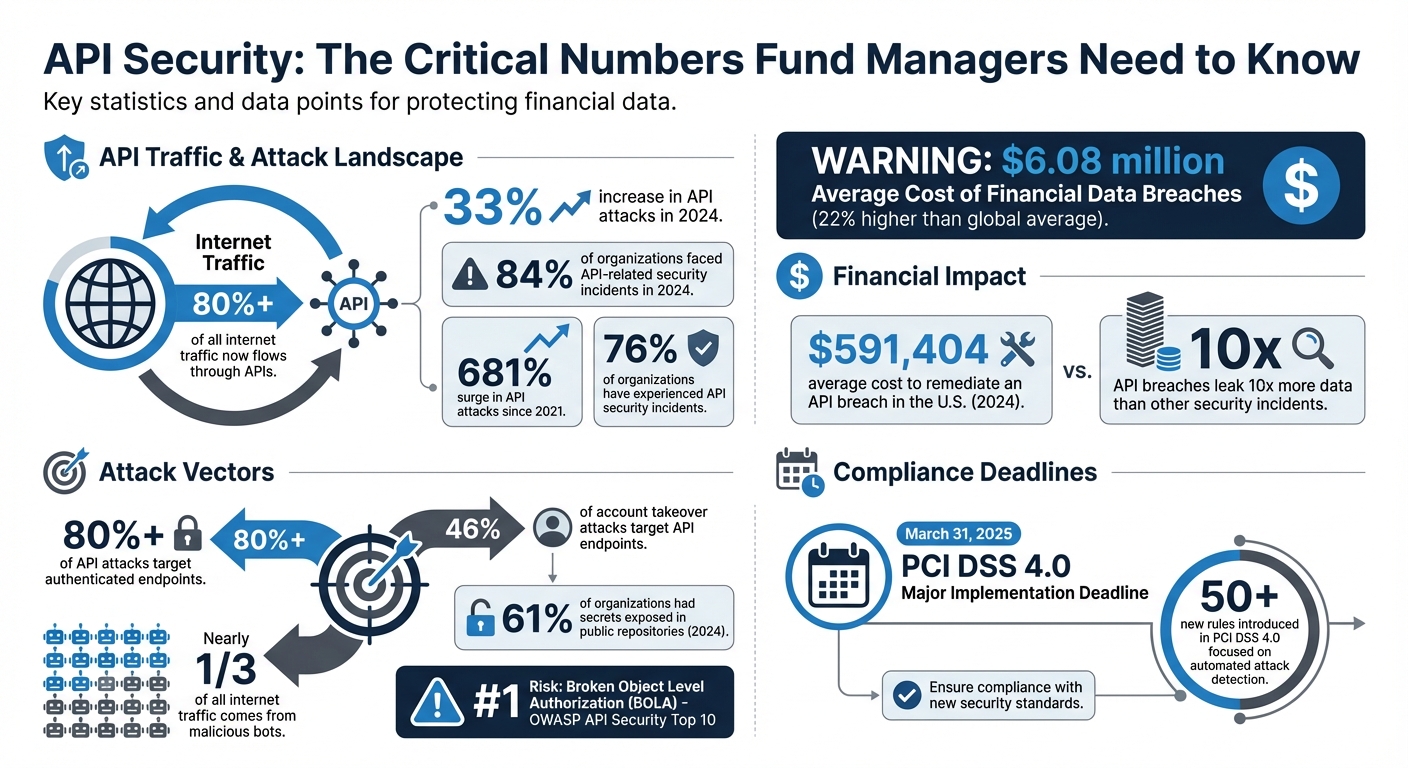
APIs are the backbone of modern fund management but are also a growing attack target. APIs handle over 80% of internet traffic, enabling real-time operations like NAV calculations and investor dashboards. However, their convenience comes with risks: in 2024, 84% of organizations faced API-related security incidents, and financial breaches averaged $6.08 million in costs.
Why this matters: APIs expose sensitive financial data, from investor records to transaction histories. Attackers exploit vulnerabilities like Broken Object Level Authorization (BOLA) to manipulate workflows or access restricted data. For fund managers, regulatory compliance (e.g., GDPR, PCI DSS) and the complexity of "shadow APIs" add to the challenge.
Key strategies for securing APIs:
- Authentication & Authorization: Use OAuth 2.1 with PKCE, Mutual TLS, and Role-Based Access Control (RBAC).
- Encryption: Adopt TLS 1.3 for communications and AES-256 for stored data.
- Monitoring & Threat Detection: Implement API gateways, rate limiting, and real-time anomaly tracking.
- Input Validation: Block injection attacks with strict validation and encoding practices.
- Regulatory Compliance: Ensure adherence to GDPR, PCI DSS, and other frameworks via detailed documentation and audits.
Why fund managers should act now: With API attacks rising and compliance penalties severe, securing APIs is not optional. Protecting endpoints, monitoring activity, and maintaining documentation are critical steps to safeguard data and investor trust.
API Security Statistics and Threats for Fund Managers 2024
APISEC|CON MONEY: API Security in Real World Banking APIs
sbb-itb-9792f40
Basic Principles of API Security
When it comes to building secure APIs for fund management, there are three main priorities: confirming who can access your systems, safeguarding data during transmission and storage, and thoroughly checking all incoming and outgoing data. These measures form a strong first line of defense against most attacks targeting financial data. Let’s break these down, starting with identity verification and access control.
Authentication and Authorization
Authentication confirms identity, while authorization determines what actions are allowed. For fund managers handling sensitive investor records and transactions, getting both right is absolutely critical.
OAuth 2.1 with PKCE is the go-to standard for user-delegated access. The Proof Key for Code Exchange (PKCE) extension is now mandatory for all clients, as it prevents attackers from intercepting authorization codes [17,18]. For even stronger security, Mutual TLS (mTLS) requires both the client and server to authenticate each other with certificates. This is a requirement for Financial-grade API (FAPI) and Consumer Data Right (CDR) standards. Meanwhile, OpenID Connect (OIDC) builds on OAuth 2.0 by adding an identity layer, delivering verifiable user identity details through ID tokens [14,17].
JSON Web Tokens (JWT) are widely used for stateless authentication in distributed systems, allowing portfolio managers to access data without the need for server-side sessions. These tokens must be signed with secure algorithms like RS256 and validated for expiration, issuer, and audience on every request [14,18,19]. To minimize risk, issue short-lived access tokens (e.g., 15 minutes) and use refresh tokens for reauthentication [18,19].
Adding Multi-Factor Authentication (MFA) strengthens security further, especially for sensitive operations. Beyond that, Role-Based Access Control (RBAC) simplifies access management by assigning permissions to roles like Admin, Portfolio Manager, or Auditor [14,6]. For more nuanced control, Attribute-Based Access Control (ABAC) evaluates access based on user attributes, resource properties, and even environmental factors like IP address or time of day [6,17].
Following the Principle of Least Privilege (PoLP) is essential: grant only the minimum access needed for a user or service to perform its role [15,17]. Object-level validation ensures users can only access resources they’re authorized to, protecting against Broken Object Level Authorization (BOLA), the top risk on the OWASP API Security Top 10 list [15,17].
RBAC organizes permissions by roles, while ABAC evaluates conditions for more context-sensitive access. Additionally, OAuth scopes define broad permissions in tokens, limiting third-party application access.
Finally, avoid relying on API keys alone for user-delegated access in financial services. API keys should only identify applications, not authenticate users.
Data Encryption and Secure Communication
After verifying identities, the next step is protecting sensitive financial data. Encryption ensures confidentiality during transmission and prevents unauthorized modification or interception.
Transport Layer Security (TLS) encrypts communication between clients and API servers, shielding against man-in-the-middle attacks. With the financial industry moving toward TLS 1.3, older versions like TLS 1.0 and 1.1 should be disabled due to vulnerabilities [15,19]. Servers must use strong cipher suites (e.g., AES-GCM) and disable weak ones to counter threats like POODLE or Heartbleed [15,19]. Enforcing HTTPS and applying HSTS headers further strengthens defenses by preventing downgrade attacks [15,19].
For data at rest, encryption algorithms like AES-256 protect stored information such as account numbers and transaction records, ensuring they remain unreadable if compromised [15,19]. Highly sensitive details, like Social Security numbers, may require field-level encryption alongside transparent database encryption (TDE).
Secure cryptographic key management is critical. Store keys separately from encrypted data using Hardware Security Modules (HSMs) or Key Management Services (KMS), and automate regular key rotation. For mobile apps, implement certificate pinning to ensure they only communicate with trusted servers [15,19]. Data masking, such as displaying only the last four digits of a credit card, also reduces exposure in API responses [5,13].
"APIs now account for more than 80% of all internet traffic, making them prime targets for cyberattacks."
– Nicole Jones, StackHawk
Input Validation and Output Encoding
Finally, input validation and output encoding are essential to prevent injection attacks and data corruption. SQL, NoSQL, and command injection attacks often exploit poor input validation. Using parameterized queries and ORM frameworks ensures user input is treated as data, not executable code.
"Unvalidated input is the gateway to SQL injection, cross-site scripting (XSS), command injection, and other attack vectors."
– Nicole Jones, StackHawk
All input sources – URL parameters, query strings, headers, and request bodies – must be scrutinized. Enforce strict JSON or XML Schema validation to reject malformed payloads. Always validate server-side, even if client-side checks are in place. APIs should reject requests with unexpected or additional properties.
Using allow-lists (defining acceptable input) is more effective than deny-lists (trying to block malicious input). For example, ensure an age field only accepts numbers between 0 and 150.
Output encoding prevents Cross-Site Scripting (XSS) attacks by ensuring browsers don’t execute malicious scripts embedded in user data. Use encoding specific to the context, such as HTML, JavaScript, or URL encoding. In high-security environments, rejecting malformed input outright is often safer than attempting to sanitize it.
Even non-relational databases are vulnerable to injection attacks. Inputs should be sanitized (e.g., with tools like mongo-sanitize) to prevent query manipulation. Additionally, configure browser security headers – like X-XSS-Protection and Content-Security-Policy – for added protection.
How to Implement API Security
Protecting APIs requires centralized controls, real-time monitoring, and strict credential management. For fund managers at Charter Group Fund Administration, these steps can help secure sensitive data effectively.
API Gateways and Traffic Management
An API gateway acts as a centralized entry point for all API traffic, simplifying the enforcement of security policies like authentication, authorization, and encryption. By centralizing these controls, you reduce the risk of exposing internal infrastructure directly. Instead of securing each microservice individually, you can apply consistent security measures across the board.
Gateways also handle rate limiting and throttling to prevent service overloads and brute-force attacks. For example, endpoints handling sensitive transactions, such as fund transfers, should have stricter rate limits compared to less critical endpoints. If traffic spikes, the gateway can queue requests rather than rejecting them outright.
To further enhance security, integrate a Web Application Firewall (WAF) with your gateway to block common attacks like SQL injection and cross-site scripting (XSS). Gateways can also validate payloads instantly, rejecting malformed data before it reaches application logic. For internal communication between services, use Mutual TLS (mTLS) to ensure both sides verify each other’s credentials.
"API gateway security is a centralized security layer that protects your backend services by controlling, authenticating, and monitoring all API traffic before it reaches your applications." – Data Prixa
With APIs now making up over 80% of all internet traffic and attacks on APIs rising by 33% in 2024, gateways are a critical defense layer. Configure them to enforce TLS 1.2 or higher, disable outdated protocols, and add HTTP Strict Transport Security (HSTS) headers to ensure encrypted connections.
Real-Time Threat Monitoring and Detection
Centralizing API traffic through gateways is just the first step – real-time monitoring ensures you can detect and respond to threats as they happen. Static defenses are often insufficient, especially since over 80% of API attacks target authenticated endpoints. By establishing behavior baselines, you can flag unusual activity. For example, a sudden spike in requests from a portfolio manager’s account could indicate an issue.
Security Information and Event Management (SIEM) systems collect and analyze logs from API interactions, correlating events to identify potential breaches. Behavioral analytics tools further refine detection by learning what constitutes "normal" behavior for users and services. Alerts can be triggered by anomalies like unexpected login attempts from unusual locations or at odd hours.
With malicious bots responsible for nearly one-third of all internet traffic, automated detection tools are essential. These tools analyze request patterns, timing intervals, and header signatures to distinguish legitimate activity from coordinated bot attacks.
"In Fintech, you aren’t just moving numbers; you are managing trust. A single API breach can wipe out years of brand building." – CyRAACS
To strengthen defenses, adopt a shift-left security approach by integrating automated API security testing into your CI/CD pipeline. This helps catch vulnerabilities early. Regularly audit for outdated "zombie" APIs, which often lack modern security updates and can create hidden entry points for attackers.
Session Management and Token Security
Strong authentication is just the starting point – secure session management is equally important for minimizing exploitation risks. Use OAuth 2.0 servers to issue tokens, ensuring they have short lifespans and strict expiration policies. For third-party access, issue opaque tokens, and for internal services, use JSON Web Tokens (JWTs) with PKCE extensions and automatic rotation. Refresh tokens can further limit exposure in case of compromise.
Avoid embedding API keys or tokens in client-side code, URLs, or version control systems. A 2024 study revealed that 61% of organizations had secrets exposed in public repositories. Instead, store sensitive credentials securely using tools like HashiCorp Vault or AWS Secrets Manager. For browser-based applications, apply the Backend-for-Frontend (BFF) pattern to keep tokens out of the browser, managing sessions with secure, HTTP-only cookies.
To enforce least privilege, limit token scopes. For instance, a token with read access should not allow write operations. Regularly review API key usage and revoke access when roles change or employees leave. Always validate token signatures, expiration, and issuer for every request, and never cache authentication states. Use JSON Web Key Sets (JWKS) for seamless signing key rotation without service disruptions.
"Just a single exposed credential or broken auth flow can open the door. The good news? Most API security issues are preventable." – Nicole Jones, StackHawk
Finally, log all authentication attempts – both successful and failed – to identify potential brute-force or privilege escalation attempts.
Regulatory Compliance and Security Audits
Building on the API security strategies discussed earlier, compliance and audit practices are essential for protecting fund managers from evolving threats. For those operating in offshore jurisdictions like the Cayman Islands, adhering to standards such as FATCA, CRS, and PCI DSS is a legal requirement.
Compliance Standards for Fund Managers
Fund managers must navigate a complex web of regulatory frameworks, each with specific API security requirements. For instance, PCI DSS 4.0, with a major implementation deadline of March 31, 2025, introduced over 50 new rules focused on automated solutions to detect and block web-based attacks.
For funds handling cross-border investor data, GDPR mandates "data protection by design." This means APIs must include encryption and access controls from the start. Additionally, GDPR requires documenting all third-party API processors – critical for funds that rely on external administrators or custodians. Meanwhile, PSD2 in Europe enforces Strong Customer Authentication (SCA) and secure communication protocols like TLS for payment-related APIs.
API security also plays a central role in FATCA and CRS compliance, providing the technical foundation for Automatic Exchange of Information (AEOI). Secure APIs protect sensitive account and transaction data shared with tax authorities – like the Cayman Tax Information Authority – through encryption and strong authentication. They also automate due diligence processes, enabling checks against public data and the IRS GIIN list.
"Financial services organizations now spend $6.08 million on average dealing with data breaches, which is 22% higher than the global average." – IBM’s 2024 Cost of a Data Breach Report
Comprehensive API logs are crucial for compliance with CRS and FATCA. These logs must track who accessed data, what was accessed, and when, and are typically retained for seven years to meet financial regulations. A robust auditing process ensures ongoing validation of your API’s security measures.
How to Conduct Security Audits and Risk Assessments
A structured approach is key to effective API security audits. Start by cataloging all APIs – this includes public, private, and third-party APIs. Pay special attention to "Shadow APIs" (those deployed without security team awareness) and "Zombie APIs" (deprecated endpoints still active). You can’t secure what you don’t know exists.
Next, evaluate your current security measures. This includes reviewing authentication methods (e.g., OAuth 2.0, mTLS), authorization controls (checking for BOLA or IDOR vulnerabilities), encryption protocols (TLS 1.3), rate-limiting settings, and logging practices. Use automated vulnerability scanning weekly or continuously, and conduct penetration tests at least once a year or after major infrastructure changes. With API attacks increasing by 681% in 2021 and 76% of organizations experiencing incidents, continuous monitoring is essential.
Before deploying new security tools, run Proof of Concept (PoC) testing in real-world conditions to ensure compatibility and effectiveness. Prevention is far more cost-effective than dealing with a breach – the average cost to remediate an API breach in the U.S. was $591,404 in 2024.
Develop a risk register to rank vulnerabilities as Critical, High, Medium, or Low. Address Critical issues immediately, High within 7 days, Medium within 30 days, and Low within 90 days. Combine short-term fixes like rate limiting with long-term improvements, such as enforcing least privilege access policies.
| Audit Component | Frequency | Tools/Methods |
|---|---|---|
| Vulnerability Scanning | Weekly/Continuous | OWASP ZAP, Burp Suite, APIsec |
| Penetration Testing | Annual (Minimum) | Manual testing, Red Teaming |
| Log Review | Daily | SIEM, Datadog, Splunk |
| Dependency Updates | Monthly | Software Composition Analysis (SCA) |
| API Discovery/Inventory | Continuous | WAF logs, Automated discovery tools |
Daily log reviews are a must – an unusual spike in data requests, for instance, could signal an impending breach. Regular audits not only help identify risks but also provide valuable insights for creating compliance documentation for stakeholders.
Documenting API Security for Stakeholders
Documentation is your strongest evidence during regulatory audits, proving that security measures are in place and working effectively. Certain regulations, like PSD2, explicitly require financial institutions to maintain up-to-date API documentation, including technical details, security protocols, and integration guidelines.
For fund managers at Charter Group Fund Administration, clear documentation demonstrates strong API governance, reassuring both investors and regulators. This is especially critical under frameworks like NIS 2, which now hold C-suite executives personally accountable for compliance failures. Documentation serves as a "defensible record" showing leadership has exercised due diligence.
"Documentation alone does not satisfy compliance. Organizations must demonstrate operational enforcement through audit trails and monitoring." – Danielle Barbour, Regulatory Compliance Author
Maintain a complete API inventory that includes all public, private, and third-party APIs to ensure no endpoints are overlooked during testing. Tools that generate documentation from API definitions, like OpenAPI Specification, can help keep technical details current. Additionally, document all third-party services handling personal data via APIs to meet GDPR Article 25 requirements.
In incident response scenarios, detailed documentation of data flows and processing activities is crucial for meeting tight notification deadlines. Even when delegating AEOI compliance to external providers, fund managers must maintain clear policies and evidence of oversight, such as board resolutions or annual reviews.
Security logs should capture who accessed what data, when, and from where, and must be tamper-proof to comply with HIPAA and SOC 2 audit controls. With API breaches leaking 10 times more data on average than other security incidents, and 46% of account takeover attacks targeting API endpoints, thorough documentation is not just a regulatory checkbox – it’s a critical defense against potential threats.
Conclusion
APIs have become the backbone of modern fund operations, but they also present opportunities for attackers to exploit sensitive data. With financial breaches potentially costing millions of dollars, every API endpoint can expose proprietary trading algorithms, investor information, and transaction details to significant risk.
To mitigate these dangers, implementing a multi-layered security strategy is critical. Techniques like strong OAuth 2.0 authentication paired with mutual TLS, TLS 1.3/AES-256 encryption, and Zero Trust principles ensure that each API request is thoroughly authenticated. Additionally, real-time monitoring and rate limiting help counter threats such as DDoS attacks and unusual activity.
"It is not just about alerting investors to data breaches. If, due to a cyberattack, systems are completely shut down for a week or two, and fund managers cannot trade, they cannot fulfill their fiduciary duty to investors." – Edward Sadtler, consultant at Citi and former Head of Intellectual Property at Schulte Roth & Zabel LLP
Adhering to compliance standards like PCI DSS 4.0, PSD2, FATCA, and CRS not only ensures regulatory alignment but also strengthens operational defenses. Maintaining thorough documentation and conducting regular audits provide a clear record of due diligence, reinforcing the importance of operational vigilance.
Operational resilience thrives on consistent practices. Automated vulnerability scanning, continuous API discovery, and strict input validation are essential to prevent logical attacks that evade traditional security measures. These approaches build a strong foundation capable of adapting to ever-evolving threats while preserving system reliability.
API security is not a one-time effort – it requires constant attention. As threats grow more sophisticated, fund managers must stay proactive with regular audits and updates to their defenses. By maintaining a strong security posture, firms protect not only their data and systems but also the trust and reputation that are vital for long-term success in a competitive industry.
FAQs
What are the quickest API security fixes a fund manager can implement first?
When it comes to securing APIs quickly, fund managers can take a few targeted actions to reduce risks. Start by enabling object authentication to ensure only authorized users access specific data. Next, make sure to validate JWT tokens properly, as they play a key role in confirming user identity. It’s also critical to sanitize SQL parameters to prevent injection attacks and to set rate limits to stop abuse from excessive requests. Together, these measures can block up to 80% of attacks right away.
Another essential step is to restrict API keys and permissions. By limiting access to only what’s absolutely necessary, you minimize the chances of over-permissioning – a common and avoidable security gap.
How can I identify and remove shadow or zombie APIs in my environment?
To tackle shadow or zombie APIs, start by using automated discovery tools to pinpoint undocumented or inactive endpoints. Implementing regular API lifecycle governance – complete with deprecation workflows – helps ensure outdated APIs are retired systematically. Additionally, automated security solutions equipped with runtime-aware inventory systems and continuous monitoring play a key role in managing these risks. This proactive approach keeps your API environment secure and minimizes potential exploitation.
What API logs should I keep for audits, and how long should they be retained?
For audits, keep detailed logs of key activities such as API requests and responses, user actions, authentication events, and error reports. The length of time you should retain these logs varies depending on regulatory requirements, which can range from 6 months to several years. This largely depends on your jurisdiction and the laws that apply to your industry. Always make sure your practices align with the relevant regulations for your business and location.
